The post-quantum transition can’t be postponed any longer
Google’s new research potentially puts the entire bitcoin supply – and the very foundation of digital trust – at risk, explains Pruden.
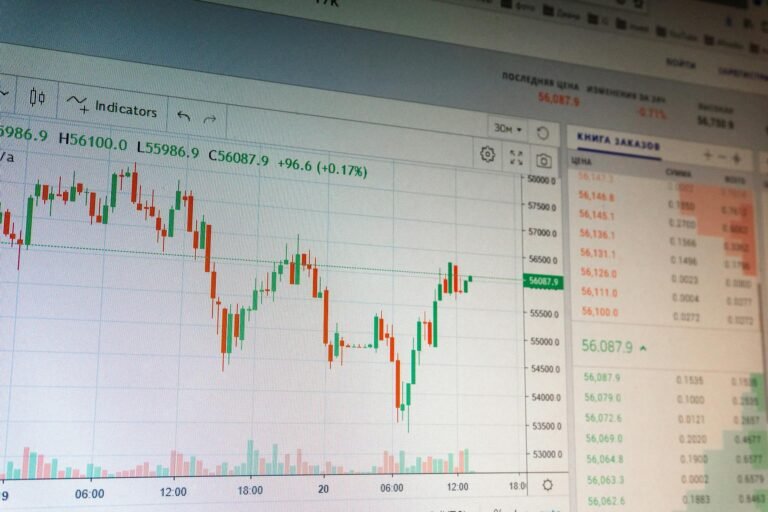
A whitepaper published yesterday by Google Quantum AI shows that a fast-clock quantum computer (with similar architecture to their existing Willow chip) could derive a private key from an exposed public key in approximately nine minutes. Bitcoin settles a block every 10 minutes.
That is, on average, a one-minute margin between the system working and an adversary hijacking live transactions directly from the mempool before they confirm. That multi-trillion dollar minute means that not just Satoshi’s coins, but the entire supply of Bitcoin now and forever is at risk.
For years, the industry’s position on quantum has been some version of “we’ll deal with it when it’s real.” Even for those who took this threat seriously, most believed that the first real threat to Bitcoin was at least a decade away, and would come in the form of “long-range” attacks on dormant assets. This paper, the latest in a string of accelerating breakthroughs make that position untenable.
This research presents a seismic shift that violently accelerates the timeline. The implications for the digital asset ecosystem are acute. If we do not coordinate an urgent upgrade effort immediately, digital assets as we know them may not be viable.
The pace of change is accelerating
Historically, estimates suggested we would need tens of millions of physical qubits running a trillion error-corrected operations to threaten Bitcoin. But critically, those estimates were based not on the elliptic-curve cryptography Bitcoin uses, but on an older algorithm known as RSA-2048.
Google’s whitepaper shatters those prior resource estimates with an architecture for breaking the 256-bit Elliptic Curve Discrete Logarithm Problem (ECDLP) used in Bitcoin specifically.
This paper brings the physical requirement down to fewer than half a million qubits and reduces the number of operations by multiple orders of magnitude. It achieves this using just 1,200 logical qubits at an error rate of 0.1%, a threshold that appears achievable in the near-term. Google has reportedly moved up its own quantum timelines to 2029.
More importantly, the architecture it used (superconducting) featured fast physical clock speeds. That means it isn’t just “lost” or dormant coins that are at risk; every single active Bitcoin transaction could be vulnerable to a quantum attacker snatching it directly from the mempool.
But the Google paper is not an isolated event. It is one of two converging breakthroughs.
Researchers from Oratomic announced a parallel breakthrough using neutral-atom hardware. Leveraging high-rate quantum low-density parity check (qLDPC) codes, they demonstrated that Shor’s algorithm can be executed at cryptographically relevant scales using approximately 10,000 to 22,000 reconfigurable atomic qubits. What once required millions of qubits has been compressed by orders of magnitude in just a few short years on two separate technological tracks, simultaneously.
Multiple tech trees with one target
How is it possible that quantum made little progress for so long, but we are now witnessing the timeline collapse so quickly? Simply put, small iterative improvements in physical fidelity, error correction, control architectures, and algorithm design are creating a feedback loop that compounds progress.